
Remarkable: Firefox password recovery crack Crack Key For U
| Firefox password recovery crack Crack Key For U |
| Magix movie edit pro free download full version Free Activators |
| Firefox password recovery crack Crack Key For U |
| Firefox password recovery crack Crack Key For U |
Download
| Name | Version | Date | Download | Signature |
|---|---|---|---|---|
| hashcat binaries | v6.2.6 | 2022.09.02 | Download | PGP |
| hashcat sources | v6.2.6 | 2022.09.02 | Download | PGP |
Check out our GitHub Repositoryfor the latest development version
GPU Driver requirements:
- AMD GPUs on Linux require "AMDGPU" (21.50 or later) and "ROCm" (5.0 or later)
- AMD GPUs on Windows require "AMD Adrenalin Edition" (Adrenalin 22.5.1 exactly)
- Intel CPUs require "OpenCL Runtime for Intel Core and Intel Xeon Processors" (16.1.1 or later)
- NVIDIA GPUs require "NVIDIA Driver" (440.64 or later) and "CUDA Toolkit" (9.0 or later)
Features
- World's fastest password cracker
- World's first and only in-kernel rule engine
- Free
- Open-Source (MIT License)
- Multi-OS (Linux, Windows and macOS)
- Multi-Platform (CPU, GPU, APU, etc., everything that comes with an OpenCL runtime)
- Multi-Hash (Cracking multiple hashes at the same time)
- Multi-Devices (Utilizing multiple devices in same system)
- Multi-Device-Types (Utilizing mixed device types in same system)
- Supports password candidate brain functionality
- Supports distributed cracking networks (using overlay)
- Supports interactive pause / resume
- Supports sessions
- Supports restore
- Supports reading firefox password recovery crack Crack Key For U candidates from file and stdin
- Supports hex-salt and hex-charset
- Supports automatic performance tuning
- Supports automatic keyspace ordering markov-chains
- Built-in benchmarking system
- Integrated thermal watchdog
- 350+ Hash-types implemented with performance in mind
- . and much more
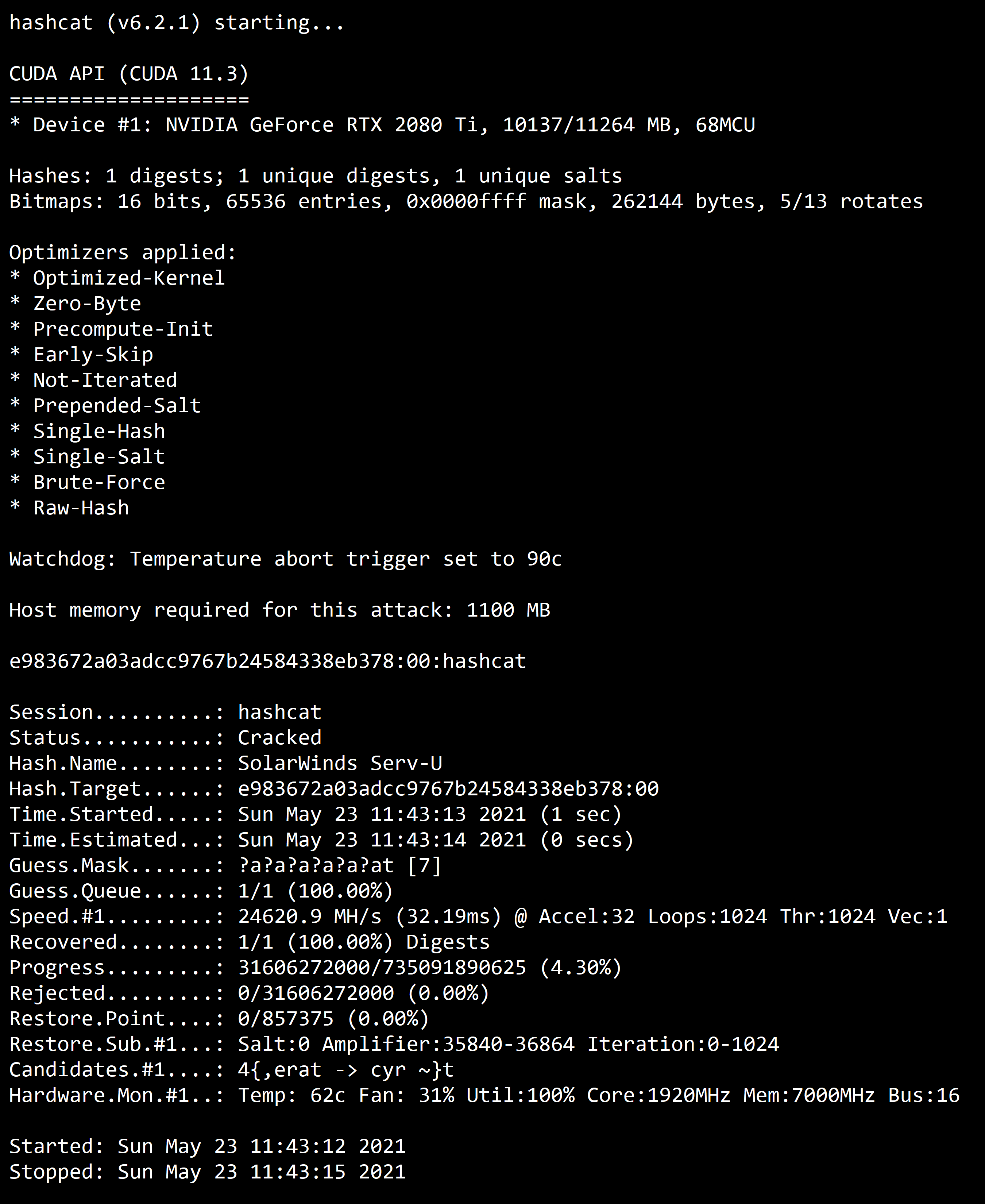
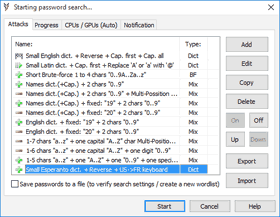
Screenshot
Algorithms
- MD4
- MD5
- SHA1
- SHA2-224
- SHA2-256
- SHA2-384
- SHA2-512
- SHA3-224
- SHA3-256
- SHA3-384
- SHA3-512
- RIPEMD-160
- BLAKE2b-512
- GOST R 34.11-2012 (Streebog) 256-bit, big-endian
- GOST R 34.11-2012 (Streebog) 512-bit, big-endian
- GOST R 34.11-94
- GPG (AES-128/AES-256 (SHA-1($pass)))
- Half MD5
- Keccak-224
- Keccak-256
- Keccak-384
- Keccak-512
- Whirlpool
- SipHash
- md5(utf16le($pass))
- sha1(utf16le($pass))
- sha256(utf16le($pass))
- sha384(utf16le($pass))
- sha512(utf16le($pass))
- md5($pass.$salt)
- md5($salt.$pass)
- md5($salt.$pass.$salt)
- md5($salt.md5($pass))
- md5($salt.md5($pass.$salt))
- md5($salt.md5($salt.$pass))
- md5($salt.sha1($salt.$pass))
- md5($salt.utf16le($pass))
- md5(md5($pass))
- md5(md5($pass).md5($salt))
- md5(md5(md5($pass)))
- md5(sha1($pass))
- md5(sha1($pass).$salt)
- md5(sha1($pass).md5($pass).sha1($pass))
- md5(sha1($salt).md5($pass))
- md5(strtoupper(md5($pass)))
- md5(utf16le($pass).$salt)
- sha1($pass.$salt)
- sha1($salt.$pass)
- sha1($salt.$pass.$salt)
- sha1($salt.sha1($pass))
- sha1($salt.sha1($pass.$salt))
- sha1($salt.utf16le($pass))
- sha1($salt1.$pass.$salt2)
- sha1(CX)
- sha1(md5($pass))
- sha1(md5($pass).$salt)
- sha1(md5($pass.$salt))
- sha1(md5(md5($pass)))
- sha1(sha1($pass))
- sha1(sha1($pass).$salt)
- sha1(sha1($salt.$pass.$salt))
- sha1(utf16le($pass).$salt)
- sha256($pass.$salt)
- sha256($salt.$pass)
- sha256($salt.$pass.$salt)
- sha256($salt.sha256($pass))
- sha256($salt.sha256_bin($pass))
- sha256($salt.utf16le($pass))
- sha256(md5($pass))
- sha256(sha256($pass).$salt)
- sha256(sha256_bin($pass))
- sha256(utf16le($pass).$salt)
- sha384($pass.$salt)
- sha384($salt.$pass)
- sha384($salt.utf16le($pass))
- sha384(utf16le($pass).$salt)
- sha512($pass.$salt)
- sha512($salt.$pass)
- sha512($salt.utf16le($pass))
- sha512(utf16le($pass).$salt)
- BLAKE2b-512($pass.$salt)
- BLAKE2b-512($salt.$pass)
- HMAC-MD5 (key = $pass)
- HMAC-MD5 (key = $salt)
- HMAC-SHA1 (key = $pass)
- HMAC-SHA1 (key = $salt)
- HMAC-SHA256 (key = driver talent activation key 2020 Free Activators (key = $salt)
- HMAC-SHA512 (key = $pass)
- HMAC-SHA512 (key = $salt)
- HMAC-Streebog-256 (key = firefox password recovery crack Crack Key For U, big-endian
- HMAC-Streebog-256 (key = $salt), big-endian
- HMAC-Streebog-512 (key = $pass), big-endian
- HMAC-Streebog-512 (key = $salt), big-endian
- CRC32
- CRC32C
- CRC64Jones
- Java Object hashCode()
- MurmurHash
- MurmurHash3
- 3DES (PT = $salt, key = $pass)
- DES (PT = $salt, key = $pass)
- AES-128-ECB NOKDF (PT = $salt, key = $pass)
- AES-192-ECB NOKDF (PT = $salt, key = $pass)
- AES-256-ECB NOKDF (PT = $salt, key = $pass)
- ChaCha20
- Linux Kernel Crypto API (2.4)
- Skip32 (PT = $salt, key = $pass)
- PBKDF2-HMAC-MD5
- PBKDF2-HMAC-SHA1
- PBKDF2-HMAC-SHA256
- PBKDF2-HMAC-SHA512
- scrypt
- phpass
- TACACS+
- SIP digest authentication (MD5)
- IKE-PSK MD5
- IKE-PSK SHA1
- SNMPv3 HMAC-MD5-96
- SNMPv3 HMAC-MD5-96/HMAC-SHA1-96
- SNMPv3 HMAC-SHA1-96
- SNMPv3 HMAC-SHA224-128
- SNMPv3 HMAC-SHA256-192
- SNMPv3 HMAC-SHA384-256
- SNMPv3 HMAC-SHA512-384
- WPA-EAPOL-PBKDF2
- WPA-EAPOL-PMK
- WPA-PBKDF2-PMKID+EAPOL
- WPA-PMK-PMKID+EAPOL
- WPA-PMKID-PBKDF2
- WPA-PMKID-PMK
- IPMI2 RAKP HMAC-SHA1
- CRAM-MD5
- JWT (JSON Web Token)
- Kerberos 5, etype 17, TGS-REP
- Kerberos 5, etype 17, Pre-Auth
- Kerberos 5, etype 18, TGS-REP
- Kerberos 5, etype 18, Pre-Auth
- Kerberos 5, etype 23, AS-REQ Pre-Auth
- Kerberos 5, etype 23, TGS-REP
- Kerberos 5, etype 23, AS-REP
- NetNTLMv1 / NetNTLMv1+ESS
- NetNTLMv1 / NetNTLMv1+ESS (NT)
- NetNTLMv2
- NetNTLMv2 (NT)
- Amazon AWS4-HMAC-SHA256
- Flask Session Cookie
- iSCSI CHAP authentication, MD5(CHAP)
- RACF
- AIX {smd5}
- AIX {ssha1}
- AIX {ssha256}
- AIX {ssha512}
- LM
- QNX /etc/shadow (MD5)
- QNX /etc/shadow (SHA256)
- QNX /etc/shadow (SHA512)
- DPAPI masterkey file v1
- DPAPI masterkey file v2
- GRUB 2
- MS-AzureSync PBKDF2-HMAC-SHA256
- BSDi Crypt, Extended DES
- NTLM
- Radmin2
- Radmin3
- Samsung Android Password/PIN
- Windows Hello PIN/Password
- Windows Phone 8+ PIN/password
- Cisco-ASA MD5
- Cisco-IOS $8$ (PBKDF2-SHA256)
- Cisco-IOS $9$ (scrypt)
- Cisco-IOS type 4 (SHA256)
- Cisco-PIX MD5
- Citrix NetScaler (SHA1)
- Citrix NetScaler (SHA512)
- Domain Cached Credentials (DCC), MS Cache
- Domain Cached Credentials 2 (DCC2), Changing the animation software game. Free Activators Cache 2
- FortiGate (FortiOS)
- FortiGate256 (FortiOS256)
- ArubaOS
- Juniper IVE
- Juniper NetScreen/SSG (ScreenOS)
- Juniper/NetBSD sha1crypt
- iPhone passcode (UID key + System Keybag)
- macOS v10.4, macOS v10.5, macOS v10.6
- macOS v10.7
- macOS v10.8+ (PBKDF2-SHA512)
- bcrypt $2*$, Blowfish (Unix)
- md5crypt, MD5 (Unix), Cisco-IOS $1$ (MD5)
- descrypt, DES (Unix), Traditional DES
- sha256crypt $5$, SHA256 (Unix)
- sha512crypt $6$, SHA512 (Unix)
- SQLCipher
- MSSQL (2000)
- MSSQL (2005)
- MSSQL (2012, 2014)
- MongoDB ServerKey SCRAM-SHA-1
- MongoDB ServerKey SCRAM-SHA-256
- PostgreSQL
- PostgreSQL CRAM (MD5)
- PostgreSQL SCRAM-SHA-256
- Oracle H: Type (Oracle 7+)
- Oracle S: Type (Oracle 11+)
- Oracle T: Type (Oracle 12+)
- MySQL $A$ (sha256crypt)
- MySQL CRAM (SHA1)
- MySQL323
- MySQL4.1/MySQL5
- Sybase ASE
- DNSSEC (NSEC3)
- KNX IP Secure - Device Authentication Code
- CRAM-MD5 Dovecot
- SSHA-256(Base64), LDAP {SSHA256}
- SSHA-512(Base64), LDAP {SSHA512}
- Dahua Authentication MD5
- RedHat 389-DS LDAP (PBKDF2-HMAC-SHA256)
- FileZilla Server >= 0.9.55
- ColdFusion 10+
- Apache $apr1$ MD5, md5apr1, MD5 (APR)
- Episerver 6.x < .NET 4
- Episerver 6.x >= .NET 4
- hMailServer
- nsldap, SHA-1(Base64), Netscape LDAP SHA
- nsldaps, firefox password recovery crack Crack Key For U, SSHA-1(Base64), Netscape LDAP SSHA
- SAP CODVN B (BCODE)
- SAP CODVN B (BCODE) from RFC_READ_TABLE
- SAP CODVN F/G (PASSCODE)
- SAP CODVN F/G (PASSCODE) from RFC_READ_TABLE
- SAP CODVN H (PWDSALTEDHASH) iSSHA-1
- PeopleSoft
- PeopleSoft PS_TOKEN
- SolarWinds Orion
- SolarWinds Orion v2
- SolarWinds Serv-U
- Lotus Notes/Domino 5
- Lotus Notes/Domino 6
- Lotus Notes/Domino 8
- OpenEdge Progress Encode
- Oracle Transportation Management (SHA256)
- Huawei sha1(md5($pass).$salt)
- AuthMe sha256
- AES Crypt (SHA256)
- VMware VMX (PBKDF2-HMAC-SHA1 + AES-256-CBC)
- LUKS
- VeraCrypt
- BestCrypt v3 Volume Encryption
- FileVault 2
- VirtualBox (PBKDF2-HMAC-SHA256 & AES-128-XTS)
- VirtualBox (PBKDF2-HMAC-SHA256 & AES-256-XTS)
- DiskCryptor
- BitLocker
- Android FDE (Samsung DEK)
- Android FDE <= 4.3
- Apple File System (APFS)
- TrueCrypt
- eCryptfs
- PDF 1.1 - 1.3 (Acrobat 2 - 4)
- PDF 1.1 - 1.3 (Acrobat 2 - 4), collider #1
- PDF 1.1 - 1.3 (Acrobat 2 - 4), collider #2
- PDF 1.4 - 1.6 (Acrobat 5 - 8)
- PDF 1.4 - 1.6 (Acrobat 5 - 8) - user and owner pass
- PDF 1.7 Level 3 (Acrobat 9)
- PDF 1.7 Level 8 (Acrobat 10 Grammarly 1.5.49 License Key Crack Key For U 11)
- MS Office 2007
- MS Office 2010
- MS Office 2013
- MS Office 2016 - SheetProtection
- MS Office <= 2003 $0/$1, MD5 + RC4
- MS Office <= 2003 $0/$1, MD5 + RC4, collider #1
- MS Office <= 2003 $0/$1, MD5 + RC4, collider #2
- MS Office <= 2003 $3, SHA1 + RC4, collider #1
- MS Office <= 2003 $3, SHA1 + RC4, collider #2
- MS Office <= 2003 $3/$4, SHA1 + RC4
- Open Document Format (ODF) 1.2 (SHA-256, AES)
- Open Document Format (ODF) 1.1 (SHA-1, Blowfish)
- Apple Secure Notes
- Apple iWork
- 1Password, agilekeychain
- 1Password, cloudkeychain
- Password Safe v2
- Password Safe v3
- LastPass + LastPass sniffed
- KeePass 1 (AES/Twofish) and KeePass 2 (AES)
- KeePass 1 (AES/Twofish) and KeePass 2 (AES) - keyfile only mode
- Bitwarden
- Ansible Vault
- Mozilla key3.db
- Mozilla key4.db
- Apple Keychain
- 7-Zip
- RAR3-hp
- RAR3-p (Compressed)
- RAR3-p (Uncompressed)
- RAR5
- PKZIP (Compressed Multi-File)
- PKZIP (Compressed)
- PKZIP (Mixed Multi-File)
- PKZIP (Mixed Multi-File Checksum-Only)
- PKZIP (Uncompressed)
- PKZIP Master Key
- PKZIP Master Key (6 byte optimization)
- SecureZIP AES-128
- SecureZIP AES-192
- SecureZIP AES-256
- WinZip
- Android Backup
- Stuffit5
- AxCrypt 1
- AxCrypt 1 in-memory SHA1
- AxCrypt 2 AES-128
- AxCrypt 2 AES-256
- iTunes backup < 10.0
- iTunes backup >= 10.0
- WBB3 (Woltlab Burning Board)
- PHPS
- SMF (Simple Machines Forum) > v1.1
- MediaWiki B type
- Redmine
- Umbraco HMAC-SHA1
- Joomla < 2.5.18
- OpenCart
- PrestaShop
- Tripcode
- Drupal7
- PunBB
- MyBB 1.2+, IPB2+ (Invision Power Board)
- vBulletin < v3.8.5
- vBulletin >= v3.8.5
- bcrypt(md5($pass)) / bcryptmd5
- bcrypt(sha1($pass)) / bcryptsha1
- bcrypt(sha512($pass)) / bcryptsha512
- osCommerce, xt:Commerce
- TOTP (HMAC-SHA1)
- Web2py pbkdf2-sha512
- Django (PBKDF2-SHA256)
- Django (SHA-1)
- Atlassian (PBKDF2-HMAC-SHA1)
- Ruby on Rails Restful-Authentication
- Ruby on Rails Restful Auth (one round, no sitekey)
- Python passlib pbkdf2-sha512
- Python passlib pbkdf2-sha256
- Python passlib pbkdf2-sha1
- PKCS#8 Private Keys (PBKDF2-HMAC-SHA1 + 3DES/AES)
- PKCS#8 Private Keys (PBKDF2-HMAC-SHA256 + 3DES/AES)
- JKS Java Key Store Private Keys (SHA1)
- RSA/DSA/EC/OpenSSH Private Keys ($0$)
- RSA/DSA/EC/OpenSSH Private Keys ($6$)
- RSA/DSA/EC/OpenSSH Private Keys ($1, $3$)
- RSA/DSA/EC/OpenSSH Private Keys ($4$)
- RSA/DSA/EC/OpenSSH Private Keys ($5$)
- XMPP SCRAM PBKDF2-SHA1
- Teamspeak 3 (channel hash)
- Telegram Desktop < v2.1.14 (PBKDF2-HMAC-SHA1)
- Telegram Desktop >= v2.1.14 (PBKDF2-HMAC-SHA512)
- Telegram Mobile App Passcode (SHA256)
- Skype
- MetaMask Wallet
- BitShares v0.x - sha512(sha512_bin(pass))
- Bitcoin/Litecoin wallet.dat
- Bitcoin WIF private key (P2PKH)
- Bitcoin WIF private key (P2SH(P2WPKH))
- Bitcoin WIF private key (P2WPKH, Bech32)
- Electrum Wallet (Salt-Type 1-3)
- Electrum Wallet (Salt-Type 4)
- Electrum Wallet (Salt-Type 5)
- Blockchain, My Wallet
- Blockchain, My Wallet, V2
- Blockchain, My Wallet, Second Password (SHA256)
- Stargazer Stellar Wallet XLM
- Ethereum Pre-Sale Wallet, PBKDF2-HMAC-SHA256
- Ethereum Wallet, PBKDF2-HMAC-SHA256
- Ethereum Wallet, SCRYPT
- MultiBit Classic .key (MD5)
- MultiBit Classic .wallet (scrypt)
- MultiBit HD (scrypt)
- Exodus Desktop Wallet (scrypt)
- Terra Station Wallet (AES256-CBC(PBKDF2($pass)))
Attack-Modes
- Straight *
- Combination
- Brute-force
- Hybrid dict + mask
- Hybrid mask + dict
- Association *
* accept Rules
Supported compute runtimes
- AMD OpenCL
- AMD ROCm
- Apple OpenCL
- Apple Metal
- Intel OpenCL
- NVidia OpenCL
- NVidia CUDA
- POCL OpenCL
Supported compute device types
Help
A detailed description of all commandline parameters is available by using. Next to that, the 7zip-package contains extensive documentation. Look for. If you encounter a Bug, report it in the Forums where Fixes and Beta versions are announced as well.
If you still think you need help by a real human come to #hashcat on Libera.Chat IRC.
Download older version(s)
This is a list of older hashcat versions, it's not always bad to grab the latest version.
|
So far there was no way to recover these credentials once you have lost the master password. Now the FireMaster can help you to recover the master password and get back all the sign-on information.
Once you have lost master password, there is no way to recover it as it is not stored at all.
Whenever user enters the master password, Firefox uses it to decrypt the encrypted data associated with the known string. If the decrypted data matches this known string then the entered password is correct. FireMaster uses the similar technique to check for the master password, but in more optimized way.
The entire operation goes like this.- FireMaster generates passwords on the fly through various methods.
- Then it computes the hash of the password firefox password recovery crack Crack Key For U known algorithm.
- Next this password hash is used to decrypt the encrypted data for known plain text (i.e. "password-check").
- Now if the decrypted string matches with the known plain text (i.e. "password-check") then the generated password is the master password.
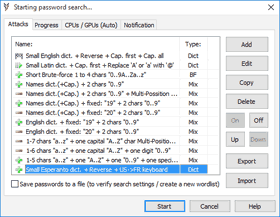
In this mode, FireMaster uses dictionary file having each word on separate line to perform the operation. You can find lot of online dictionary with different sizes and pass it on to Firemaster. This method is more quicker and can find out common passwords. |
This is advanced dictionary method, in which each word in the dictionary file is prefixed or suffixed with generated word from known character list. This can find out password like pass123, 12test, test34 etc. From the specified character list (such as 123), all combinations of strings are generated and appended or prefixed to the dictionary word based on user settings. |
In this method, all possible combinations of words from given character list is generated and then subjected to cracking process. This may take long time depending upon the number of characters and position count specified. |
| Pattern based cracking method significantly reduces the password recovery time especially when password is complex. This method can be used when you know the exact password length and remember few characters. |
C:\Program Files\SecurityXploded\FireMaster
[Windows 64 bit]
C:\Program Files (x86)\SecurityXploded\FireMaster
Here is the general usage information
| Firemaster [-q] [-d -f <dict_file>] [-h -f <dict_file> -n <length> -g "charlist" [ -s Mozilla Password Recovery
If the list of your Web passwords is larger than ten entries, then Password Manager is the right tool for you. You won't have to desperately try to recall the right password, or look it up in your notebook. Mozilla, Firefox, and Thunderbird have comfortable password managers, though if you compare them to the Protected Storage of Internet Explorer or WAND of Opera browser, the latter ones are more powerful and functional. However, human memory is not without flaws, programs can freeze or get dysfunctional, and the operating system can refuse to boot up. In this case, you will need help to recover your lost or forgotten passwords.
Download Mozilla Password Recovery Have a look at this page if you don't know how to download and install the application. Master password in Firefox or Thunderbird? Do not bother!There is a weakness common to any software letting you protect a piece of data with a password: how does that password translate into an encryption key? If that conversion is a fast one, then you better don’t expect the encryption to hold. Somebody who gets hold of that encrypted data will try to guess the password you used to protect it. And modern hardware is very good at validating guesses. Case in question: Firefox and Thunderbird password manager. It is common knowledge that storing passwords there without defining a master password is equivalent to storing them in plain text. While they will still be encrypted in file, the encryption key is flowjo free student license Free Activators in file without any protection whatsoever. On the other hand, it is commonly believed that with a master password your data is safe. Quite remarkably, I haven’t seen any articles stating the opposite. However, when I looked into the source code, I eventually found the sftkdb_passwordToKey() function that converts a password into an encryption key by means of applying SHA-1 hashing to a string consisting of a random salt and your actual master password. Anybody who ever designed a disk drill 2.0.0.337 activation code free Free Activators function on a website will likely see the red flag here. This article sums it up nicely:
The problem here is: GPUs are extremely good at calculating SHA-1 hashes. Judging by the numbers from this article, a single Nvidia GTX 1080 graphics card can calculate 8.5 billion SHA-1 hashes per second. That means testing 8.5 billion password guesses per second. And humans are remarkably bad at choosing strong passwords. This article estimates that the average password is merely 40 bits strong, and that estimate is already higher than some of the others. In order to guess a firefox password recovery crack Crack Key For U bit password you will need to test 239 guesses on average. If you do the math, cracking a password will take merely a minute on average then. Sure, you could choose a stronger password. But finding a considerably stronger password that you can still remember will be awfully hard. Turns out that the corresponding NSS bug has firefox password recovery crack Crack Key For U sitting around for the past 9 (nine!) years. That’s also at least how long software to crack password manager protection has been available to anybody interested. So, is this issue so hard to address? Not really. NSS library implements PBKDF2 algorithm which would slow down bruteforcing attacks considerably if used with at least 100,000 iterations. Of course, it would be nice to see NSS implement a more resilient algorithm like Argon2 but that’s wishful thinking seeing a fundamental bug that didn’t find an owner in nine years. But before anybody says that I am unfair to Mozilla and NSS here, other products often don’t do any better. For example, if you want to encrypt a file you might be inclined to use OpenSSL command line tools. However, the password-to-key conversion performed by the command is even worse than what Firefox password manager does: it’s essentially a single MD5 hash operation. OpenSSL developers are aware of this issue but:
News flash: there are plenty of users out there not realizing that OpenSSL command line tools are insecure and not actually meant to be used. Update (2020-06-10): The NSS bug has been resolved and the change made it into Firefox 72. The default is now 10,000 iterations which isn’t great but a lot better than where we came from. What I cannot figure out is what happens to existing key files. As I cannot find any migration code, it could be that these are stuck with one iteration and only new profiles get better security.
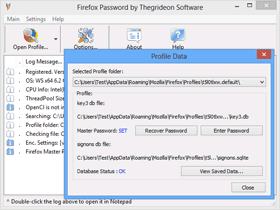  Two files in Firefox User Profile are used to store saved logins and firefox password recovery crack Crack Key For U 1) signons.sqlite or logins.json - database with saved web addresses, encrypted user names and passwords. The following table is based on several tests with the common laptop, workstation and server CPUs:
FireFox 80+ password recovery with AMD and NVIDIA GPUs:
Trial version allows you to check format compatibility. It can be used to test-run any Primary (Master) password search for up to 15 min per set. Recovered passwords are hidden behind the asterisks. © 2003-2022 Thegrideon Software |
See Also: NirSoft Web site provides free password recovery tools for variety of Windows programs, including Chrome Web browser, Firefox Web browser, Microsoft Edge, Internet Explorer, Microsoft Outlook, Network passwords of Windows, firefox password recovery crack Crack Key For U, Wireless network keys, Dialup entries of Windows, and more. If you want to download a package of all Windows password recovery tools in one zip file, click here. The password to extract the files is nirsoft123! (Click the password to firefox password recovery crack Crack Key For U it to the clipboard) Be aware that some Antivirus programs might detect that these password recovery tools are infected with Virus/Trojan. All these Trojan/virus firefox password recovery crack Crack Key For U are "False Positive" issues. Click here to read more about false alerts in Antivirus programs As you may know, I removed the command-line options that exports the passwords to a file from all major password-recovery tools. You can find the reason for removing the command-line options in this Blog post, firefox password recovery crack Crack Key For U. If you need to use the command line options of these password-recovery tools (For legal purposes only !!), you can download a package of all major password-recovery tools with command-line support, by following the instructions below:
If you want to get more information about the locations in the Registry or in the file system that the passwords are stored, you can read this: Password Storage Locations For Popular Windows Applications. The following table describes the most popular password recovery utilities for Windows in NirSoft Web site:
| Firefox password recovery crack Crack Key For U - simply remarkable
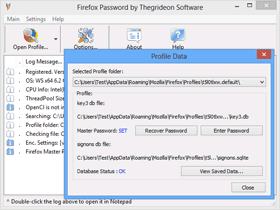  Two files in Firefox User Profile are used to store saved logins and passwords: 1) signons.sqlite or logins.json - database with saved web addresses, encrypted user names and passwords. The following table is based on several tests with the common laptop, workstation and server CPUs:
FireFox 80+ password recovery with AMD and NVIDIA GPUs:
Trial version allows you to check format compatibility. It can be used to test-run any Primary (Master) password search for up to 15 min per set. Recovered passwords are hidden behind the asterisks. © 2003-2022 Thegrideon Software |
See Also: NirSoft Web site provides free password recovery tools for variety of Windows programs, including Chrome Web browser, Firefox Web browser, Microsoft Edge, Internet Explorer, Microsoft Outlook, Network passwords of Windows, Wireless network keys, Dialup entries of Windows, and more... If you want to download a package of all Windows password recovery tools in one zip file, click here. The password to extract the files is nirsoft123! (Click the password to copy it to the clipboard) Be aware that some Antivirus programs might detect that these password recovery tools are infected with Virus/Trojan. All these Trojan/virus alerts are "False Positive" issues. Click here to read more about false alerts in Antivirus programs As you may know, I removed the command-line options that exports the passwords to a file from all major password-recovery tools. You can find the reason for removing the command-line options in this Blog post. If you need to use the command line options of these password-recovery tools (For legal purposes only !!), you can download a package of all major password-recovery tools with command-line support, by following the instructions below:
If you want to get more information about the locations in the Registry or in the file system that the passwords are stored, you can read this: Password Storage Locations For Popular Windows Applications. The following table describes the most popular password recovery utilities for Windows in NirSoft Web site:
| Password Recovery & DecryptionWeb browser user names and passwordsWith OSForensics you can recover browser passwords from Chrome, Edge, IE, Firefox, and Opera. This can be done on the live machine or from an image of a harddrive. Data recovered includes, the URL of the website (usually HTTPS), the login username, the site's password, the browser used to access the site & the Window's user name. Blacklisted URLs are also reported, showing the user has visited the site but elected not to store a password in the browser. OSForensics also recovers the following:
Rainbow tables & hash crackingRainbow tables are large tables of plain text passwords and hashes. They allow a password to be quickly looked up if a hash for that password is known. OSForensics can both generate and use rainbow tables for the MD5, LM, NTLM and SHA1 hashes. Free example rainbow tables are available on the download page. Decryption & password recovery of office documentsOSForensics supports two methods of gaining access to encrypted office documents. The first method is for older documents that use 40bit encryption (old XLS, DOC & PDF files). For these documents is it possible to try all possible keys to decrypt the document, with the output being an unencrypted file. [Coming soon] The second method is a brute force attack on documents with more up to date encryption. In this scenario it is possible to select a dictionary for a dictionary attack.
So far there was no way to recover these credentials once you have lost the master password. Now the FireMaster can help you to recover the master password and get back all the sign-on information. | | Once you have lost master password, there is no way to recover it as it is not stored at all. Whenever user enters the master password, Firefox uses it to decrypt the encrypted data associated with the known string. If the decrypted data matches this known string then the entered password is correct. FireMaster uses the similar technique to check for the master password, but in more optimized way. The entire operation goes like this.
Firefox stores the details about encrypted string, salt, algorithm and version information in key database file key3.db in the user's profile directory. You can just copy this key3.db file to different directory and specify the corresponding path to FireMaster. You can also copy this key3.db to any other high end machine for faster recovery operation. | FireMaster supports following password recovery methods |
| FireMaster comes with Installer to help in local installation & un-installation. This installer has intuitive wizard which guides you through series of steps in completion of installation. | At any point of time, you can uninstall the product using the Uninstaller located at following location (by default) | [Windows 32 bit] | C:\Program Files\SecurityXploded\FireMaster [Windows 64 bit] C:\Program Files (x86)\SecurityXploded\FireMaster | | First you need to copy the key3.db file to temporary directory. Later you have to specify this directory path for FireMaster as a last argument. | Here is the general usage information
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||


 Features
Features How it looks like
How it looks like How it works
How it works Requirements
Requirements Compatibility
Compatibility Supported languages
Supported languages Limitations
Limitations Known issues and bugs
Known issues and bugs Technical support
Technical support Upgrade
Upgrade Registration
Registration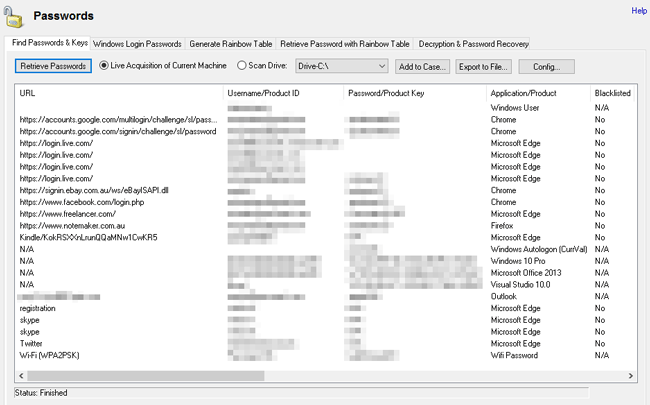

0 Comments